EXTERNAL ATTACK SURFACE MANAGEMENT
Your Attack Surface Changed Today.
Did You Notice?
New subdomains. Expired certificates. Open ports. Configuration drift. DriftAlarm monitors your external attack surface 24/7 and alerts you the moment something shifts — with AI-powered remediation guidance in plain English.
No credit card required • First scan in under 90 seconds • Plans from $99/month
Everything You Need to Defend Your Attack Surface
One platform. Complete visibility. Actionable intelligence.
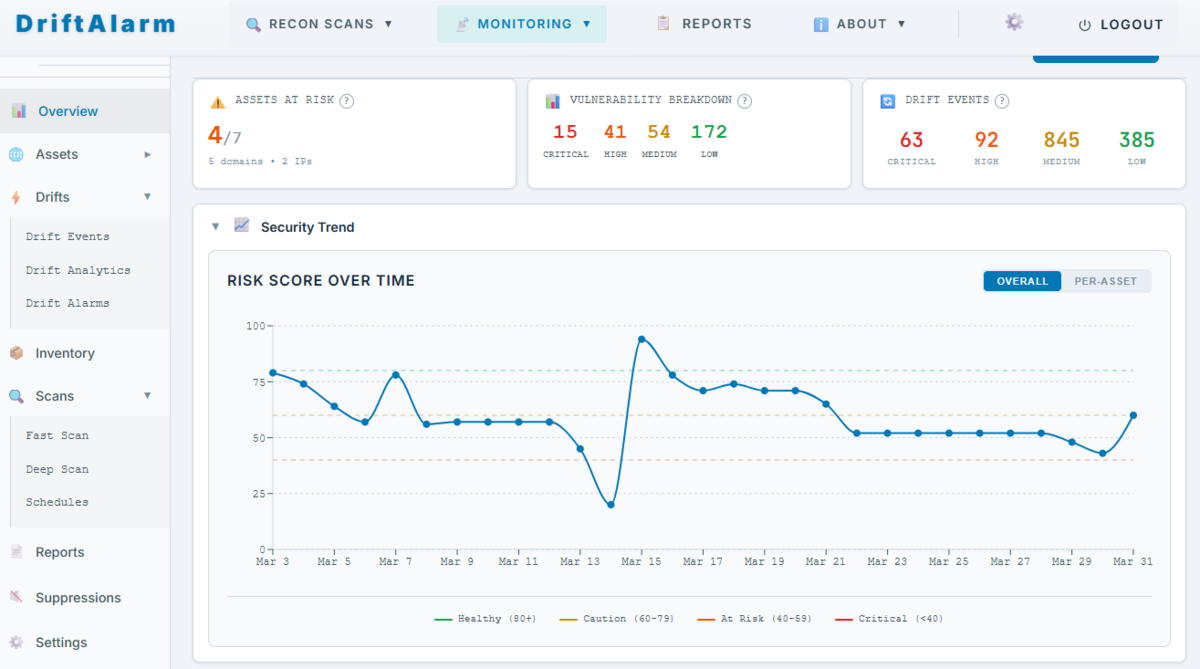
Unified Security Dashboard
Risk scores, vulnerability trends, and drift events — all in one view. Know your security posture at a glance, track improvement over time.
AI-Powered Threat Analysis
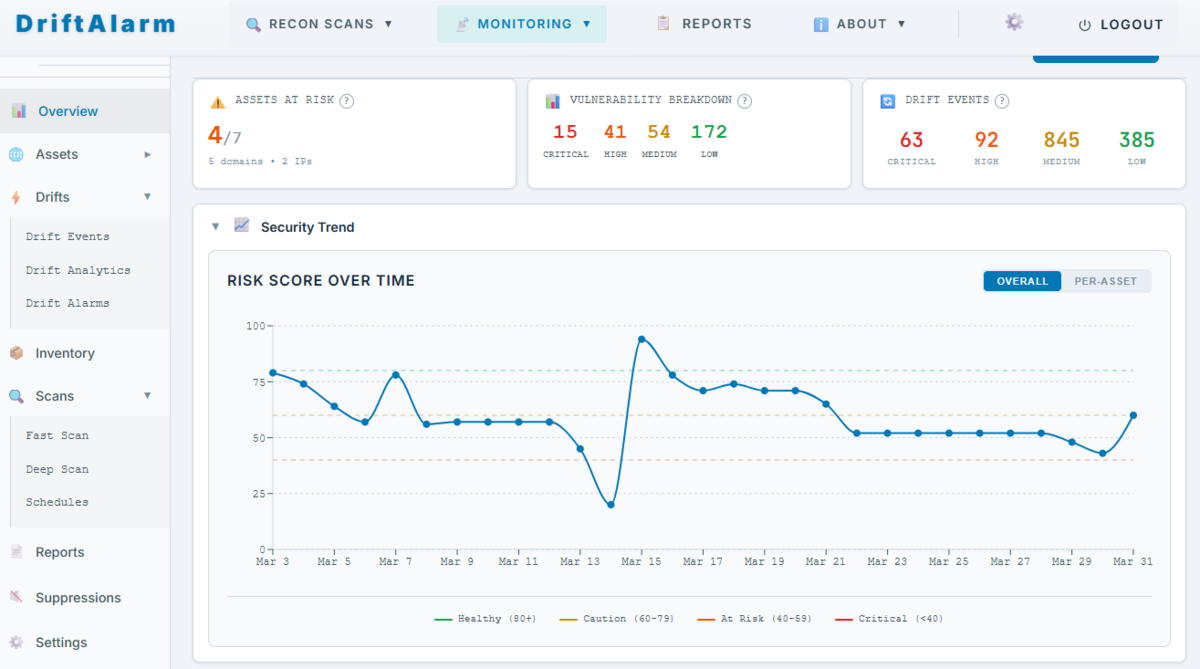
Every scan produces an AI-generated security brief with threat level, attack complexity, prioritized actions, and plain-English executive summary.
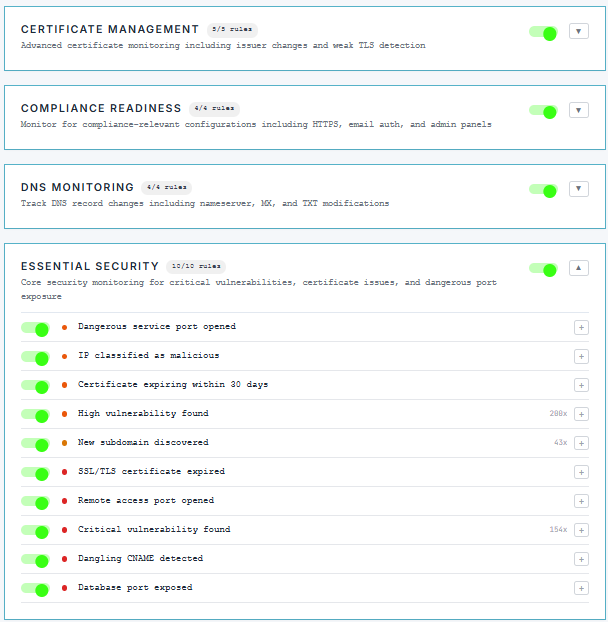
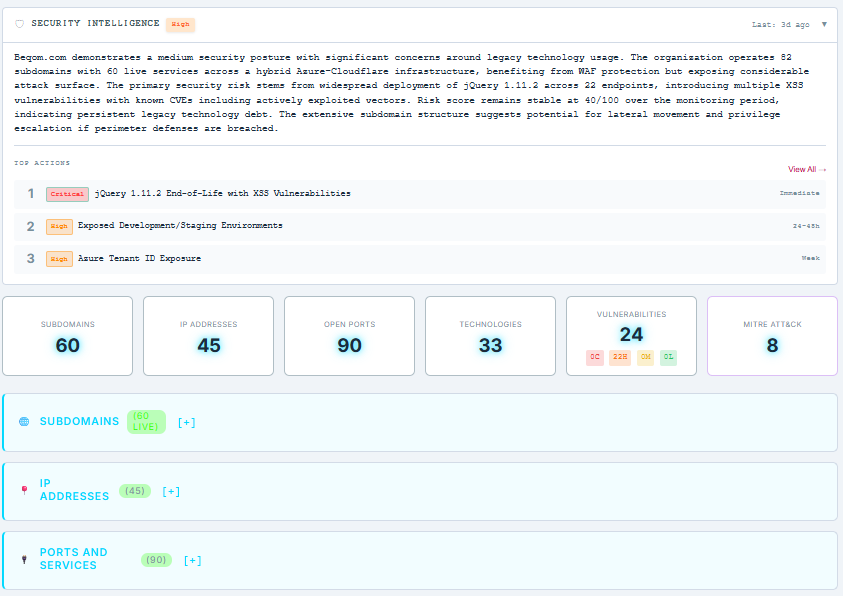
41 Rules. 8 Categories. Zero Blind Spots.
Certificate changes, DNS drift, new ports, technology updates, compliance gaps — monitored automatically. Get alerted the moment something changes.
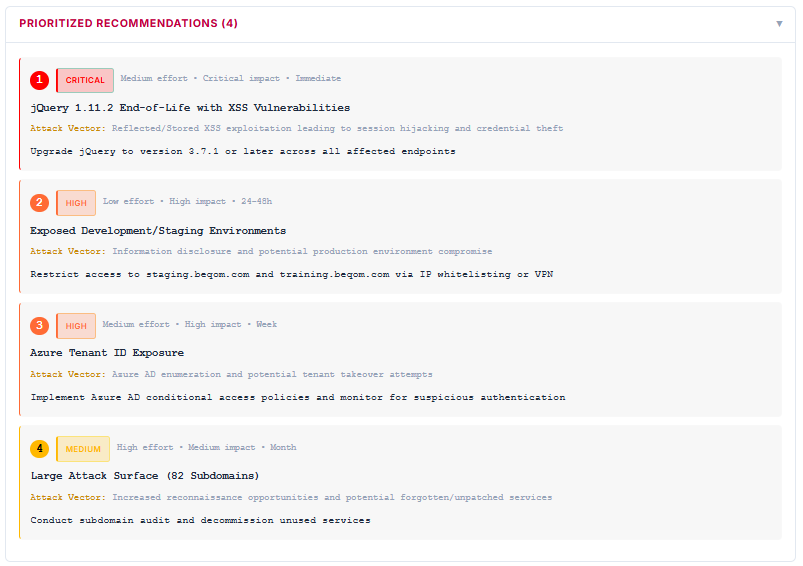
Know Exactly What to Fix First
AI-ranked recommendations with severity, effort estimate, attack vector, and specific fix instructions. No more guessing which vulnerability matters most.
Get Started in Three Steps
Add Your Domains & IPs
Enter the domains and IP ranges you want to monitor. Our scanner immediately maps your external attack surface — subdomains, open ports, services, and technologies across your entire perimeter.
"We discovered 60 live subdomains and 90 open ports across 45 IP addresses in under 3 minutes."
Automated Scanning & Drift Detection
Daily vulnerability scans and weekly deep assessments run automatically. 41 drift detection rules watch for certificate changes, DNS modifications, new services, and compliance gaps — alerting you the moment something shifts.
"845 medium-severity drift events caught and tracked automatically."
Fix What Matters First
Every finding includes AI-generated remediation guidance ranked by severity, effort, and business impact. MITRE ATT&CK mapping shows how attackers could chain vulnerabilities. Compliance mapping connects findings to OWASP, CIS, and NIST frameworks.
"From scan to prioritized fix list in 90 seconds."
Set it up once. We watch continuously.
Stop Overpaying. Stop Guessing. Start Knowing.
Doing Nothing
- No visibility into what's internet-facing
- Vulnerabilities found by attackers first
- Configuration drift goes unnoticed for months
- Can't answer "are we secure?" when the board asks
- Compliance gaps discovered at audit time
Enterprise EASM
- Full attack surface discovery
- Continuous monitoring
- Vulnerability detection
- 6-month onboarding with professional services
- Requires dedicated security team to operate
- Locked into vendor ecosystem
DriftAlarm
- Full attack surface discovery
- AI-powered drift detection (41 rules, 8 categories)
- MITRE ATT&CK + OWASP + CIS + NIST mapping
- AI remediation with effort & impact scoring
- Vulnerability validation (XSS, SQLi, CORS, subdomain takeover...)
- First scan results in 90 seconds
- No sales process — start your trial now
Intelligence That Drives Action
Not just another list of CVEs. DriftAlarm shows you what matters, why it matters, and how to fix it.
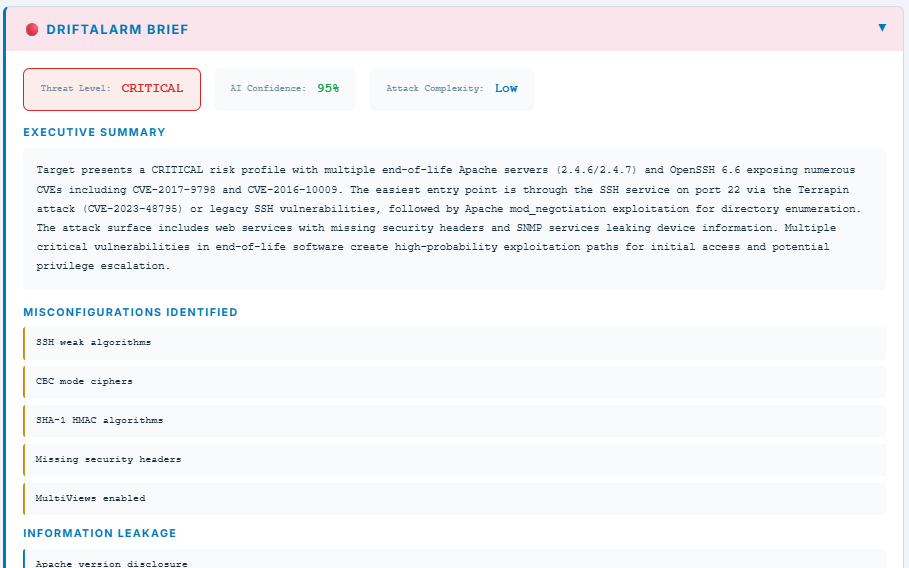
AI-Generated Security Brief
Every scan produces an executive-ready threat assessment.
- Threat level with AI confidence score
- Plain-English executive summary — no jargon
- Misconfigurations identified and categorized
- Information leakage detection
- Attack complexity rating
Share it with your board, your auditor, or your team. Your AI security analyst works 24/7.
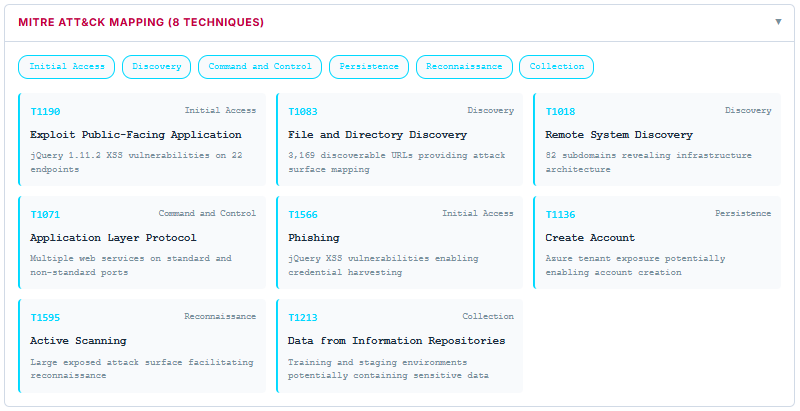
See How Attackers Would Chain Your Vulnerabilities
Every finding is mapped to the MITRE ATT&CK framework — the same methodology used by nation-state threat intelligence teams.
- Initial Access vectors identified
- Lateral movement paths mapped
- Credential access risks flagged
- Persistence opportunities highlighted
Understand not just what's vulnerable, but how an attacker would actually exploit it.
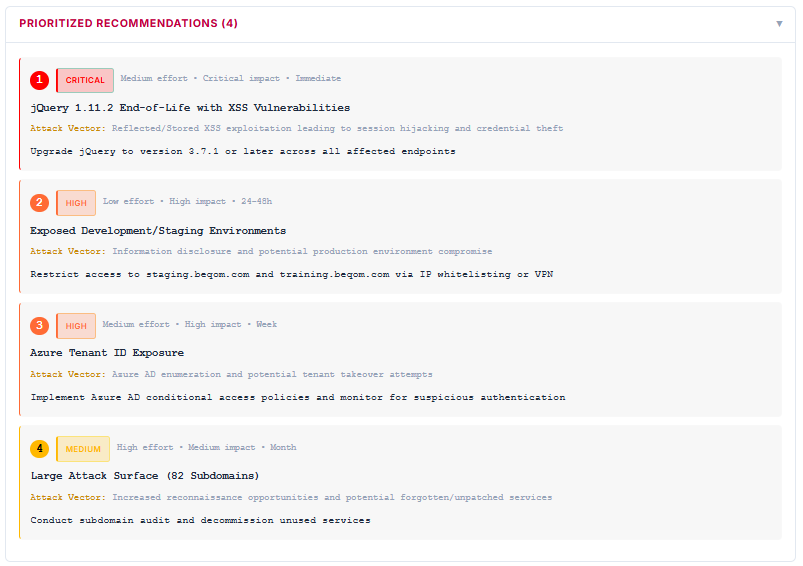
A Remediation Roadmap, Not a Data Dump
Every recommendation is ranked by:
- Severity (Critical → Low)
- Effort to fix (Low / Medium / High)
- Business impact (Critical → Medium)
- Timeline (Immediate / 24-48h / Week / Month)
Each item includes the specific attack vector and exact remediation steps for your technology stack. Fix the right things in the right order.
Board-Ready Executive Reports, Generated Automatically
Every account gets AI-generated executive security posture reports you can share with your board, auditors, or leadership team.
- Overall security grade (A through F)
- Key risk indicators with business impact context
- Trend analysis showing posture changes over time
- Prioritized recommended actions with timelines
- Compliance gap assessment (CIS, OWASP, NIST)
No more scrambling before board meetings. Your security story is always ready.
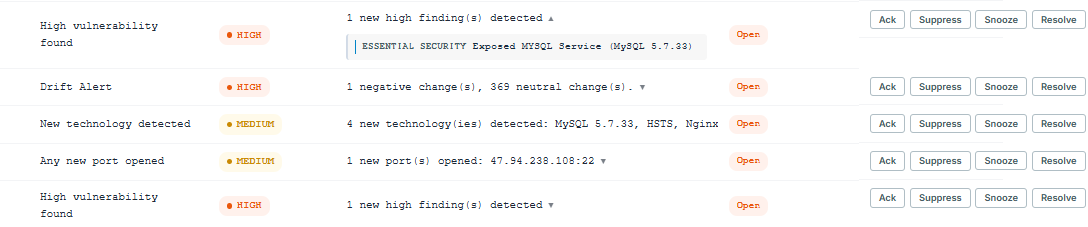
Every Change. Tracked. Actionable.
When something changes in your attack surface, DriftAlarm catches it and tells you exactly what happened:
- HIGH Exposed MySQL Service (MySQL 5.7.33) detected
- MEDIUM 4 new technologies detected: MySQL, HSTS, Nginx
- MEDIUM New port opened: 47.94.238.108:22
- DRIFT 1 negative change, 369 neutral changes
Each event can be acknowledged, suppressed, snoozed, or resolved — so your team stays focused on what matters.
Simple, Transparent Pricing
All features included at every tier. No feature gating — just choose your scale.
Standard
- ✓ 1 domain + 1 IP
- ✓ 10 Fast Scans per week
- ✓ 5 Deep Scans per week
- ✓ 3 Scheduled Scans per week
- ✓ Drift Detection & Alerts
- ✓ AI Remediation Guidance
- ✓ All AI analysis features included
Pro
- ✓ 5 domains + 10 subnets
- ✓ 50 Fast Scans per week
- ✓ 25 Deep Scans per week
- ✓ 15 Scheduled Scans per week
- ✓ Same features, 5x the scale
- ✓ AI Executive Reports
- ✓ Slack Notifications
Enterprise
- ✓ Custom domains & IPs
- ✓ Unlimited scans
- ✓ Volume pricing for large perimeters
- ✓ Priority support
- ✓ API access
- ✓ Scheduled report delivery
Every plan includes: AI Security Briefs • MITRE ATT&CK Mapping • Drift Detection (41 rules) • Compliance Mapping (OWASP, CIS, NIST) • Vulnerability Validation • Prioritized Remediation
Common Questions
Security Guides
Practical guides for IT teams defending their attack surface
AI Vulnerability Discovery
AI models can now find 181 exploits where previous models found 2. What this means for your business.
Threat IntelligenceThe Patch Window Is Dead
Time-to-exploit dropped from 63 days to negative 7. Why continuous monitoring beats annual pentests.
ReadinessAI Attack Readiness Checklist
AI-enabled attacks up 89% YoY. A 10-point checklist to assess your readiness.
FundamentalsAttack Surface Monitoring
Scope, discover, analyze, and prioritize your external exposures with a P0-P4 rubric.
Drift DetectionConfiguration Drift
How DNS changes, new ports, and TLS degradation create security gaps attackers exploit.
ChecklistAttack Surface Checklist
Weekly, monthly, and quarterly monitoring checklist for IT teams of 1-5 people.
Your Attack Surface Changed While You Read This Page.
New subdomains. Expiring certificates. Open ports. Configuration drift. It's happening right now. The only question is whether you see it first — or an attacker does.
No credit card • No sales call • Full Standard access for 30 days